Now hiring!

The Real-World Asset (RWA) market now has over $30 billion tokenized on-chain, with treasuries, private credit, and commodities driving adoption. At the same time, major institutions are actively deploying tokenized products
But this growth raises a fundamental question: how do you secure a digital token that represents rights to a physical asset governed by traditional property law?
Securing RWAs is different from securing native crypto assets. Tokenized real-world assets must satisfy both blockchain security requirements and traditional legal protections. Whether an RWA system holds up under stress depends on whether these two systems remain aligned.
The "security" of an RWA is a dual-linkage problem. If the link between the digital token and the physical asset breaks, the token becomes a "worthless digital orphan."

Institutional-grade RWA security requires three interdependent pillars:
A failure in one can render the others ineffective.
Tokenizing real-world assets creates a legal bridge between two systems that were never designed to interact. Physical assets are governed by property law and regulatory oversight. Tokens are governed by cryptographic rules embedded in a blockchain ledger.
To evaluate the strength of this bridge, it is useful to distinguish between three types of tokens:
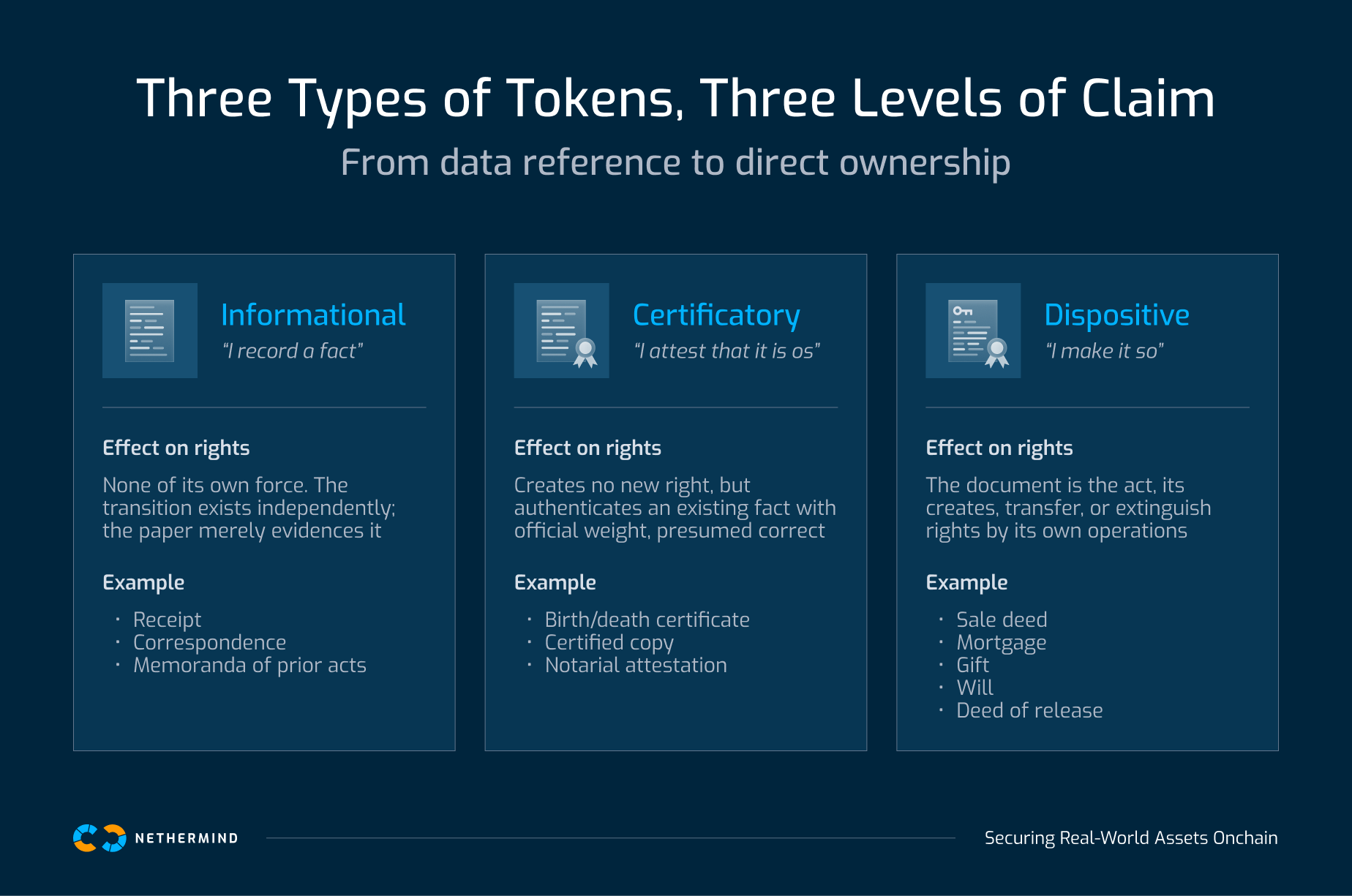
In practice, most tokenized assets today provide contractual claims rather than direct ownership. Courts will typically prioritize centralized registries and legal agreements over decentralized ledgers. Understanding this distinction determines whether a token represents true ownership or simply a digital wrapper around a centralized asset.
Tokenization is as much a legal problem as a technical one. The infrastructure for issuing tokens exists, but regulatory frameworks remain fragmented, particularly across jurisdictions.
Three legal trends are shaping institutional RWA systems.
The technical layer secures the tokenized asset on-chain.
Institutional tokenization platforms typically use modular smart contract architectures that separate core functions such as issuance, compliance checks, and asset management. This allows components to be independently audited and upgraded.
Custody and key management systems commonly rely on Multi-Party Computation (MPC) and Hardware Security Modules (HSMs) to eliminate single points of failure. Independent audits verify both smart contract security and the integrity of custody infrastructure. For systems where correctness guarantees matter at the code level, formal verification provides a stronger baseline than audits alone.
Another critical component is the connection between on-chain records and off-chain assets. Proof-of-Reserve systems verify that the assets backing a token exist and match the circulating token supply.
In addition, oracle systems supply external data required for asset valuation, collateral monitoring, and liquidation logic. Using multiple independent data feeds helps reduce manipulation risk and improves reliability.
These technical systems must remain aligned with the legal structures that define asset ownership.
In practice: securing tokenized vaults at scale.
Lagoon Protocol builds tokenized vault infrastructure on Ethereum using ERC-7540 async vaults. As the protocol grew past $300M in TVL, Nethermind Security conducted sequential audits across five versions, tracking how new features changed accounting assumptions and identifying state transition risks between pending and settled assets before they reached production. Read the case study →
The operational layer ensures that the digital representation of an asset continues to match the physical reality.
This involves regular audits and reconciliation processes to confirm that assets remain in custody and correspond to the tokens issued on-chain. Without these processes, platforms risk creating ghost assets: tokens that exist on the blockchain while the underlying asset has been sold, damaged, or otherwise compromised.
Operational security also includes incident response procedures, custody oversight, and monitoring systems that track changes across legal and technical environments.
Institutional RWA platforms increasingly rely on identity-linked asset ownership rather than purely wallet-based systems.
Instead of anonymous transfers, wallets are connected to verified identities through cryptographic claims. These claims can confirm attributes such as investor accreditation or jurisdictional eligibility without exposing personal information on-chain.
Standards such as ERC-3643 implement this model by embedding identity checks directly into token transfers.
Key capabilities include:
Combining identity-based tokens with zero-knowledge proofs can allow platforms to enforce compliance requirements while preserving user privacy.
One of the most important legal questions for RWAs is what happens if the issuer fails.
Modern tokenization platforms address this risk through bankruptcy-remote Special Purpose Vehicles (SPVs) that legally isolate assets from the issuer’s corporate balance sheet. If the issuing company becomes insolvent, the underlying assets remain protected from its creditors.
As tokenized assets scale, risks increasingly arise from the interaction between on-chain and off-chain systems. Oracle manipulation, custodian outages, and reconciliation failures can cascade across layers of infrastructure.
Security models are therefore shifting from point-in-time audits toward continuous monitoring across legal, technical, and operational systems.
Regulatory clarity is gradually improving. The EU’s MiCA regulation establishes a framework for crypto-asset issuance and service providers, while jurisdictions such as Singapore, Hong Kong, and the UAE are developing tokenization-specific regulations.
However, global harmonization remains a long-term process, particularly for cross-border asset ownership.
The viability of tokenized real-world assets depends on more than smart contract security. Legal enforceability, technical infrastructure, and operational oversight are not separate workstreams, they are a single system. A failure in any one layer can undermine the others.
As tokenized assets scale into the trillions, the platforms that get this right will not just be more secure. They will be the infrastructure.
If you're building tokenized asset infrastructure, Nethermind works across the full stack. Talk to the team.